As cyber-attacks become more and more common, protecting your personal data is becoming increasingly difficult. There are so many ways one could access one of your accounts. If you use that account to login into your social media, you are doomed.
Why? Because nearly all known password reset links are sent via email. If a malicious individual has full access to that email, they can use it to reset passwords on all the accounts. Hence, you will be locked out of your email and all the accounts, as mentioned earlier.
We know this doesn't sound very comforting, so some measures can help prevent this catastrophe from happening. One such measure is two-factor authentication which we will talk about today. In this guide, we will explain everything about two-factor authentication and how you can use it in your system.
What is Two-Factor Authentication?
Two-factor authentication adds an extra security level when you log into a website, online bank account, credit card portal, or any other site. Almost any website with a system with users will have single-factor authentication with a username and a password. Sometimes, however, even the strongest of passwords are not enough to keep an important account secure.

Two-factor authentication, as can be guessed from the name, requires one extra step to log into a website or access an online account. First, you will have to enter the username and password to get to the second step. Then the site will, in most cases, send you a text message or email with a verification code that you will have to enter into the site to get access to the account.
How Two-Factor Authentication Works?
Understanding the inner workings of Two Factor Authentication (2FA) is crucial to appreciating its effectiveness in safeguarding your online presence.
Explaining the Concept of "Factors" in Authentication
Authentication is the process of confirming a user's identity. In this context, authentication revolves around the notion of "factors," which are the elements used to verify who you are. So if you’re wondering what is 2FA code, these factors serve as the building blocks of 2FA:
- Knowledge Factor: This factor pertains to something the user knows. It typically involves information that only the user should possess, such as a password, PIN, or a specific piece of knowledge.
- Possession Factor: Possession factors involve something the user has in their physical possession, like a security token, a mobile device, a smart card, or even an authentication app.
- Inherence Factor: Inherence factors are characteristics inherent to the user's physical self. These include biometric traits such as fingerprints, facial recognition, voice patterns, and even behavioral biometrics like keystroke dynamics or gait.
Overview of the Three Types of Factors
Each of these factors plays a distinct role in authentication:
- Knowledge Factor: Knowledge factors authenticate users based on information stored in their memory. It verifies what you know, such as a password or PIN, making it the most common factor in single-factor authentication.
- Possession Factor: Possession factors confirm the user's identity by validating something they have in their possession. This can be a physical object like a security token or a virtual possession like a smartphone app that generates one-time codes.
- Inherence Factor: Inherence factors rely on physical characteristics unique to individuals. These factors authenticate users based on who they are, utilizing biometric data like fingerprints, facial features, or voice patterns. Inherence factors provide a high level of security because they are challenging to duplicate.
Step-by-Step Process of 2FA Verification
The verification process in 2FA unfolds systematically to ensure a higher level of security:
- User Initiation: The process typically begins when a user attempts to log in to a website or application that requires 2FA. They enter their username and, in most cases, their password as the first factor, the knowledge factor.
- Factor 1 (Knowledge Factor): The system validates the user's identity by checking the first factor, typically a password. If the entered credentials match the stored data, the system proceeds to the next step.
- Factor 2 (Possession or Inherence Factor): Here comes the crucial second factor, which falls into either the possession or inherence category. The user is prompted to provide this factor, which could be in the form of:
- A Security Token: The user may need to use a physical token, smart card, or mobile app to generate a one-time code.
- Biometric Data: Alternatively, the user might provide biometric data, such as a fingerprint scan or facial recognition.
- Authentication Confirmation: Upon successful validation of the second factor, the user is authenticated and granted access to the website or application. The presence of two factors ensures a significantly higher level of security, making it challenging for malicious actors to gain unauthorized access.
By requiring these two distinct factors, 2FA significantly bolsters your online security, mitigating the risks associated with single-factor authentication methods and enhancing your protection against unauthorized access.
How does Two-Factor Authentication Help?
Aside from the methods of attack mentioned previously, there are still countless ways to gain access to your accounts. Two-factor authentication adds an extra step of security to prevent a malicious individual who has gotten access to your password from being able to log in to the account.
What Threats are Out There?
Before getting into preventative measures, we need to identify what exactly we should care about. Even if you have a very strong password, there are ways hackers could get access to your accounts without even ever having it through things like phishing scams and installing keyloggers on your machine.
Cracking Weak Passwords with Brute Force Attacks
If your password is just a word followed by some numbers, especially if it is not very long, hackers can brute force it. What does that mean? They run a script that attempts every single combination of characters and numbers until they get it right.
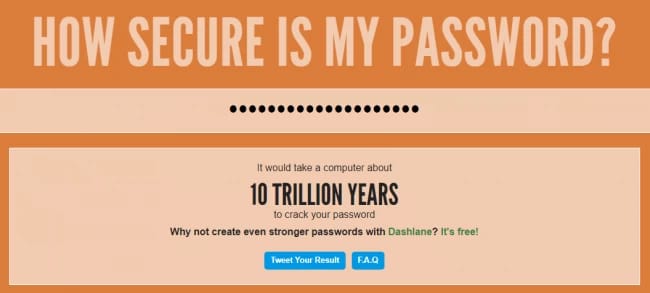
There is a way to test whether your password is susceptible to this style of attack with tools such as HOW SECURE IS MY PASSWORD?, which will tell you approximately how long it would take a computer to crack your password.
Please note that you should not enter your same password into these tools, but one of similar characters and format. For example, if your password is 777monovm@Pa55, then enter 936tokern#Rk67. As you can see, they are completely different to our eyes, but to a computer that is trying to crack it, they would be about the same since they consist of the same character types in the same positions.
Dictionary Attacks
Whenever you read any suggestions for creating a strong password, they always mention not including any words within a dictionary. This is because hackers can run scripts that enter every word in the dictionary and even try different combinations of said words. Therefore if your password is catsarecute, such an attack would crack it within minutes.
Keyloggers
This is one nasty virus that you can catch while browsing the web. It simply runs in the background upon startup, records every keypress that you do, and shares it with the attacker. Not only are your passwords in danger, but your entire private conversations.
Phishing Scams
These attacks are a bit different from the rest, they do not actually install any malware or run any malicious scripts. These are sites on the internet that are nearly identical to legitimate popular sites such as Facebook and Twitter. Once you try to log in, however, they do nothing and send the login information you used to the attackers’ database.
Types of Two-Factor Authentication Methods
Two-factor authentication (2FA) offers a variety of methods to strengthen your online security. Each method adds an additional layer of protection to verify your identity. Let's explore the four primary types of 2FA methods:
SMS-Based Authentication
SMS-based 2FA, also known as text message authentication, is one of the most common and user-friendly methods. It relies on your mobile phone for verification:
- Setup: When you enable SMS-based 2FA, you link your mobile phone number to your account.
- Verification: After entering your username and password, the system sends a one-time verification code to your mobile device via SMS.
- Input Code: You receive the code and enter it into the login screen.
- Access Granted: If the code matches, you gain access to your account.
Pros:
- Easy to set up and use.
- No need for additional apps or hardware.
Cons:
- Vulnerable to SIM card hijacking and interception.
- Less secure than app-based methods.
Authenticator Apps
Authenticator apps offer more secure and convenient examples of 2 Factors method. Popular apps like Google Authenticator, Authy, and Microsoft Authenticator generate time-based one-time passwords (TOTPs):
- Installation: Download and install your chosen authenticator app from the app store.
- Account Setup: Add your accounts to the app by scanning QR codes or entering setup keys provided by the service.
- Code Generation: The app generates a new code every few seconds.
- Code Input: When logging in, enter the current code displayed in the app.
Pros:
- Increased security compared to SMS-based 2FA.
- Works offline, enhancing reliability.
Cons:
- Requires installation of a separate app.
- Backup and recovery options are essential in case of device loss.
Biometric Authentication
Biometric authentication leverages unique physical characteristics to verify your identity. Common biometric factors include:
- Fingerprint Recognition: Your device scans your fingerprint for authentication.
- Facial Recognition: Using your device's camera, it analyzes your facial features.
- Iris or Retina Scanning: Highly advanced systems use the unique patterns of your iris or retina.
- Voice Recognition: Analyzing your voice patterns and characteristics.
Pros:
- Highly secure, as biometric data is difficult to replicate.
- Convenient and user-friendly.
Cons:
- Requires compatible hardware (e.g., fingerprint sensor, facial recognition camera).
- Possible privacy concerns regarding biometric data storage.
Hardware Tokens and Security Keys
Hardware tokens and security keys offer the highest level of security but require physical devices:
- Hardware Tokens: These small, physical devices generate one-time passwords that you enter during login.
- Security Keys: These USB or NFC devices provide cryptographic proof of your identity.
Pros:
- Exceptionally secure and resistant to hacking.
- Ideal for high-security environments.
Cons:
- Costly and not as user-friendly for everyday use.
- Risk of losing the physical token.
Choosing the right 2FA method depends on your security needs and preferences. SMS-based authentication and authenticator apps are suitable for most users, while biometric methods and hardware tokens are ideal for those requiring the highest level of protection. By implementing 2FA, you significantly enhance your online security, making it much more challenging for unauthorized individuals to access your accounts.
Implementing Two-Factor Authentication
Enabling Two-Factor Authentication (2FA) is a powerful step toward enhancing your online security. In this section, we'll explore how to implement 2FA across various online services, provide step-by-step guides for setting it up, and highlight best practices for managing and securing your 2FA credentials.
Enabling 2FA for Popular Online Services
Email Services:
- Gmail: Google offers robust 2FA options. Navigate to your Google Account settings, click on "Security," and follow the prompts under "2-Step Verification."
- Outlook: Microsoft provides 2FA through its Authenticator app or SMS. Enable it in your Outlook account settings.
Social Media:
- Facebook: Access your Facebook Security Settings and click on "Use two-factor authentication" to set it up using an authentication app or your phone number.
- Twitter: Visit your Twitter account's "Security and account access" settings to enable 2FA using an authentication app or SMS.
Banking and Financial Services:
- Online Banking: Many banks now offer 2FA. Contact your bank's customer service or visit their website for guidance on enabling it.
- Payment Apps: Services like PayPal and Venmo offer 2FA options in their security settings.
Step-by-Step Guides for Setting Up 2FA on Different Platforms
Mobile Apps:
- Google Authenticator:
- Install the app on your smartphone.
- Add an account by scanning a QR code or entering a setup key.
- The app generates time-based one-time passwords (TOTPs) for 2FA.
- Authy:
- Install Authy from your app store.
- Create an account or sign in.
- Follow the app's instructions to add accounts and enable 2FA.
Social Media Platforms (Using Facebook as an Example):
- Log in to your Facebook account.
- Navigate to "Settings & Privacy" > "Settings."
- Click on "Security and Login."
- Scroll down to "Two-Factor Authentication" and click "Use two-factor authentication."
- Choose between an authentication app or text message (SMS) as your 2FA method.
- Follow the on-screen instructions to complete the setup.
Best Practices for Managing and Securing 2FA Credentials
- Use a Password Manager: A password manager helps you keep track of your 2FA codes and passwords securely. Popular options include LastPass, 1Password, and Bitwarden.
- Backup Codes: Some services offer backup codes when you set up 2FA. Keep these in a secure location. They can be used to regain access if you lose your 2FA device.
- Secure Your Devices: Ensure that the devices you use for 2FA, such as smartphones, are adequately protected with PINs, fingerprints, or facial recognition.
- Keep 2FA Codes Secure: Avoid taking screenshots or photos of 2FA QR codes or backup codes. Store them in a secure, offline location.
- Avoid Using SMS: While SMS-based 2FA is better than no 2FA, it's less secure than app-based 2FA. Whenever possible, opt for app-generated codes.
By following these guidelines and enabling 2FA across your online services, you'll significantly strengthen your digital security, making it substantially more challenging for unauthorized individuals to access your accounts and personal information.
Methods of Two-Factor Authentication
There are multiple ways websites can implement two-factor authentication, and each one rolls with the method that works best for them. Here are some of the factors that different sites use.
- Knowledge Factor: This is the most commonly implemented method of 2FA (i.e., 2 Factor Authentication). Upon entering a username and password, you will need to enter a verification code sent to your mobile phone or email. Another example of this would be answering a security question that you set up when creating an account.
- Possession Factor: Probably the safest method, requiring actual hardware to log in. For instance, if you are working with highly classified data, it might be a good idea to set a physical USB key along with your computer’s password.
- Software Token Factor: These are apps that provide two-factor authentication, such as Google Authenticator.
- Biometric Factor: Either fingerprints, facial recognition, or speech patterns are used as a second factor when logging into a website.
- Location Factor: Some sites will rely on your location to confirm your identity.
Why is Two-Factor Authentication Important?
Passwords have been the mainstream form of authentication since the start of the digital revolution. But, this security measure is far from infallible. Here are some worrying facts about this traditional security measure:
- 90% of passwords can be cracked in less than six hours.
- Two-thirds of people use the same password everywhere.
- Sophisticated cyber attackers have the power to test billions of passwords every second.
The vulnerability of passwords is the main reason for requiring and using 2FA. Two-factor authentication might seem like a hassle. After all, you’ll need to take an extra step to log onto your favorite websites. Without 2FA, you could be leaving yourself vulnerable to cybercriminals who want to steal your identification, access your bank accounts, or hack into your online credit card portals.
Why? Without a complex, unique password for each of your online accounts, a skilled hacker may be able to crack your passwords. And once they do, they can easily access the personal and financial information in any accounts with that username and password combination.
Benefits of Two-Factor Authentication
2 factor authentication (2FA) offers a multitude of advantages, enhancing online security and safeguarding sensitive information.
Enhanced Security
2FA provides an additional layer of defense, bolstering protection against unauthorized access. Even if a password is compromised, the second factor serves as a formidable barrier, preventing malicious actors from gaining entry.
Mitigation of Password Vulnerabilities
2FA mitigates password-related vulnerabilities that often plague online security. It combats issues like password reuse and brute-force attacks, reducing the risk of unauthorized access.
Safeguarding Data Privacy
By fortifying authentication processes, 2FA safeguards sensitive information and preserves data privacy. It ensures that only authorized individuals can access confidential data, bolstering privacy and compliance measures.
Biometrics Two-Factor Authentication
One of the major issues with passwords and tokens is that they can't prove your identity. Biometrics solves that problem. Adding biometrics as an authentication factor is the best way to prove identity because your biometrics are you. Identity-based access control is a significant improvement over alternative authentication factors because you can't forget it, you can't lose it, and they are extremely difficult to steal and unique to you.

Biometrics are light years more secure than other authentication factors and make accessing sensitive information and remote servers easy and effective. When you utilize smartphones to deploy biometric authentication, it's easy and effective; people who complain about 2FA being a nuisance won't have anything to complain about anymore.
To make one final point, many consumers are concerned about protecting their biometrics. This is a valid concern, but if the biometrics are properly implemented, it will enhance personal and professional privacy. Using visual cryptography techniques and a distributed data model helps make sure your biometrics and sensitive information will never end up in the wrong hands. This way, you can use 2FA solutions and still sleep at night knowing your biometrics and data are safe.
Challenges and Considerations
While Two-Factor Authentication (2FA) is a formidable defense against cyber threats, it is not without its challenges and considerations. In this section, we explore the potential vulnerabilities and risks associated with 2FA, the delicate balance between security and user experience, and the importance of backup and recovery options.
Potential Vulnerabilities and Risks
While 2FA boosts security, it's not foolproof. The second factor, like a mobile device, can be stolen or exploited. Phishing attacks can trick users into revealing both factors, and provider breaches may expose user data.
Balancing Security and Convenience
Finding the right balance between security and user experience is crucial. Complex 2FA can deter users, so user-friendly methods and education are key. Offering diverse authentication options empowers users to choose what suits them.
Backup and Recovery
Planning for device loss or failure is essential. Backup codes and alternative contact methods prevent lockout, ensuring users can access their accounts. Striking a balance between security and user-friendly recovery options is vital.
Future Trends in Two-Factor Authentication
As the digital landscape evolves, so does the realm of Two-Factor Authentication (2FA). The future promises exciting advancements that will further bolster online security. Let's explore the emerging trends and the integration of 2FA with other cutting-edge security measures.
Emerging Technologies in Authentication
1. Passwordless Authentication:
Passwords have long been a weak link in online security due to their vulnerability to breaches and human error. Passwordless authentication methods aim to eliminate the need for traditional passwords altogether. Some emerging passwordless methods include:
- Biometric Authentication: Leveraging biometric data like fingerprints, facial recognition, and iris scans for seamless, secure authentication.
- FIDO (Fast Identity Online): FIDO standards enable passwordless authentication using hardware tokens or biometrics.
2. Biometric Advancements:
Biometrics continues to evolve, offering enhanced accuracy and security. Future biometric advancements may include:
- Behavioral Biometrics: Analyzing user behavior, such as typing patterns, mouse movements, and voice recognition, for continuous authentication.
- Heartbeat Authentication: Utilizing the unique patterns of an individual's heartbeat as a biometric identifier.
Integration of 2FA with Other Security Measures
1. Multi-Factor Authentication (MFA):
While 2FA is a powerful security measure, MFA takes it a step further by incorporating additional factors beyond the initial two. This can include something the user is, knows, and has, making it even more challenging for attackers to breach security.
2. Adaptive Authentication:
Adaptive authentication is a dynamic approach that assesses the risk of a login attempt in real-time and adapts security measures accordingly. It evaluates various factors, such as the user's location, device, behavior, and threat intelligence, to determine the appropriate level of authentication required. This ensures that strong authentication is reserved for high-risk scenarios while allowing smoother access for routine activities.
3. Blockchain-Based Authentication:
Blockchain technology is gaining attention as a secure means of authentication. Decentralized identity and self-sovereign identity solutions leverage blockchain to provide users with control over their identity data, enhancing privacy and security.
4. Zero Trust Security:
The Zero Trust model assumes that no user or device is inherently trustworthy, even if they are within the corporate network. Zero Trust security integrates continuous authentication and strict access controls, making it a powerful complement to 2FA.
5. IoT Authentication:
With the proliferation of Internet of Things (IoT) devices, securing them becomes paramount. Integrating 2FA and other advanced authentication methods into IoT ecosystems ensures that these devices remain secure against unauthorized access.
Conclusion
Having two-factor authentication on your accounts is still not the end-all solution to protecting your online accounts. Along with 2FA, you should also have strong passwords for all your accounts and use a different password for each one. For ease of use, we recommend using a password manager that will help you keep track of all of them.
We know you have surely heard this before, but we will stress the importance of this statement again: have your password be at least 12 characters long and include both uppercase & lowercase letters along with numbers and special characters (such as &, #, $, etc.); do not include any dictionary words or personal information within the passwords such as birthdate, name, etc.
Keeping your computer malware-free is also crucial to your online accounts' security as even certain types of 2FA can be deciphered with a keylogger. For instance, if the only type of two-factor authentication you have on one of your accounts is a security question, the keylogger will record the answer as well.
