With new developments in technology, we witness some of the greatest achievements in software integration and effective execution. The same technology is also being used to wreak havoc in many people's lives. One such security threat that many modern cyber hackers use is the Man in the Middle (MITM) attack.
This is a dangerous security threat that is constantly using the loopholes present in different high-level safety systems. People in every field of technology are concerned with this attack because hackers can run the automated software program and not be caught. Eavesdropping attacks like this are very hard to calculate and assess before it's too late.
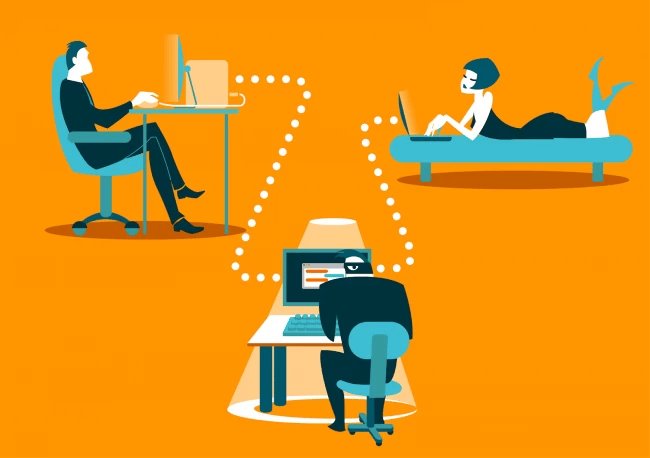
The man in the middle refers to the attacker who is trying to interrupt an ongoing conversation between two participants or data transfer between two central systems. The worst part about this attack is that participants have no idea of the middle man's existence. This is one of the most common security threats out there.
They get caught with different malicious links used to extract confidential information. The middle man not only has the power to eavesdrop and listen to the entire conversation, but he can also modify the communication to his interests.
People who pull off such attacks are also called Black Hat hackers in the world of IT. In today's article, we will illuminate several methods used by the attackers to intercept communication and learn some ways to prevent the attack from happening.
Definition of Man in the Middle (MITM) Attack

The name "man-in-the-middle" is given to the attacker who listens to a conversation between two communicating hosts. The communication channels can be connected between two clients/ servers or between a client and server.
When these channels are interrupted by a third party, then the two targets involved will be put in a vulnerable position without knowing a hacker's existence. MITM attacks are made to fulfil two main objectives: to retrieve sensitive information from either participant and/or to modify existing content in the files/servers. In simple words, a MITM attack is like your mailman trying to steal your bank card information and then sealing the cover without you having any idea about it.
It is also important to know that MITM attacks are not limited to any website or personal accounts. They can be used to get into your email accounts and online shops to use your login credentials.
How do Man-in-the-Middle Attacks Work?
MITM attacks are one o the most common cyber attacks and they always follow an order to gain information and access to personal accounts. The first step is spoofing, where the attacker exaggerates some of the characteristic features of the person he is trying to imitate.
Spoofing of an email address or phone number allows Black Hat hackers to be a part of the client and server's communication cycle. When MITM attackers become a part of the conversation, the data relays through them and reaches the other party so that they will know everything about the ongoing transfer of data. The interference could also happen via creating a fake profile or website.
The second step in this attack is the decryption phase. Here, the attacker tries to decode the communication channels' data without alerting the client or application. Some of the common ways to redirect traffic for clients are creating fake connections that mimic the same features of a well-known website or institution.
For example, a hacker can create fake chatbots to lure unsuspecting victims and feed them false information to redirect their webpage to a fake website. This is done to extract the victim's login credentials.
The final step is authentication. When the hacker has all he needs, he will authenticate his presence in front of the other victim and hijack the entire conversation. These steps can be put into automated software, and the hacker can get away if he is careful enough to pull back the malicious traffic.
Some MITM attacks are also made on public and private Wi-Fi connections, but to execute this attack perfectly, the attacker must be in close or remote proximity to the targeted network. In this scenario, it is difficult to initiate a MITM attack, but when they use DNS spoofing to replace the IP addresses, the same attacks can be made on large-scale networks.
Types of MITM Attacks
Secure connections can be attacked in multiple ways, so it is essential to know at least some of the primary MITM attacks to stay on alert and deploy the necessary tools to safeguard your server and personal information. In the previous mailman scenario, the methods are similar to ARP spoofing, IP spoofing, and DNS spoofing, but hackers use many other techniques to gain control. We have listed some main ways one can intercept your address or connection:

1. IP Address Spoofing
We know that spoofing is a way to imitate another person's characteristics. Similarly, hackers use IP address spoofing to give a wrong IP address that usually indicates another machine. In reality, IP spoofing alone will not help interception and decryption, so MITM attackers combine it with TCP sequence prediction. The sequence prediction happens in multiple steps. The first step for the attacker would be to identify internet connections associated with a transmission control protocol. In this type of network, there occurs a three-way handshake to establish or exchange a session. During the exchange, both recipients send sequence numbers to recognize respective packets. At this point, the attacker will be closely listening to the conversation or exchange of information and waits for the opportunity to send the successive sequence numbers. As he is pretending to be the original sender, the other recipient will not notice any difference. This is how IP address spoofing is done to intercept a secure connection.
2. DNS Cache Poisoning
DNS spoofing is more dangerous than ARP and IP spoofing, as it can affect a large number of victims simultaneously. It is also more challenging to execute such an attack because the attacker must have his cache vulnerable. It is called a poisoning attack because we are inserting a fake entry into the local cache of the client, so every time a client uses this cache, they will be directed to the attacker. Once the clients fall for the fake entry, the attacker again becomes the man-in-the-middle to steal data. If this method is successfully implemented, it could lead to a significant data breach.
3. IDN Homograph Attacks
IDN attack is another way to understand the encryption language. This is not for being the middle of two legitimate participants because it deals with interception of information and sending the same to another website. Black Hat hackers use this method to fake a copy of an established domain, which is then used to attract new users to the website. This is done by using a Punycode and buying an authenticated SSL certificate. These help in giving assurance to the user by seeing the locked symbol present in the address bar. As the user has no idea of the fake website, they provide all the information thinking it's real, and in the background, the hacker relays all the data to his server.
4. Stealing Browser Cookies
Browser cookies contain information about the user, and if they are in the wrong hands, they can be exploited in many ways. Hackers have the ability to hijack these browser cookies without alerting the system user. Once the cookies are transferred to another system, they can access every website and online platform without entering any personal credentials.
5. SSL Hijacking
SSL is a safety protocol used in redirecting users from an unsafe server to a secure server. This is done automatically when a user lands on a malicious site. Even after having such protocols in place, hackers find ways to hijack SSL. In most real-life use cases, we observed that SSL hijacking is implemented to make security software more adaptable to threats. These tools in security software are built to identify SSL hijacking and prevent any data extraction.
6. Wi-fi Eavesdropping
Being a man in the middle doesn't always mean interception of a conversation or communication; it can also be done by deploying a wi-fi connection. Hackers avoid getting caught by giving a legitimate name to their connection. As soon as users start connecting to this connection that they believe is secure, the attacker begins to access each individual's login credentials. That is why many people advise not to use free or public wi-fi networks.
7. Packet Injection
We have seen before that MITM attacks can use TCP sequence prediction to exchange packets between users. In a similar manner of inserting sequence numbers, hackers can also leverage monitoring tools presented in their device to send packets containing malware into mainstream communication channels. This is called packet injection, and it is malicious.
8. Client Compromise
The client is compromised when the attacker releases a trojan application into their machine. As the client is unaware of the situation, they will not be alerted, and the application continues to listen. One example of this attack is cross-site scripting on the client's most used webs.
Ways to Prevent MITM Attack
When you are under attack, you can do so little on your defence. In the same way, you need to employ more preventive measures to stop cyberattacks from happening. It is not easy to identify these attacks, but it is also not hard to create secure connections. Some of the ways to adopt are mentioned below:
- Secure Connection: The first line of defence will always be a connection with no threats attached. With secure connections, it is also suggested to deploy Secure Socket Layer (SSL) technology. By this integration, users will not be allowed to access unsecured sites, as HTTPS uses port 443 by default.
- Use a VPN: We often connect to the network that is in the closest proximity, and by doing that, we ignore the security risks attached to those public internet connections. The best alternative to that would be a VPN. Deploying a VPN on a daily basis will help in encrypting the data sent by the user on any online platform. VPNs not only act on the encryption end, but they also stop malware from infiltrating a client machine or server.
- Install Endpoint Security: Black Hat hackers always tend to find one way or another to get into your system. Even if they gain access to the device or the entire IT network, you can still use endpoint security like Kaspersky to eliminate all threats. This is your last line of defence in some cases, so choose the right software for endpoint security.
- Use Multi-Pin Authentication: Even if the hacker gets all the way to the checkout and uses your credentials, you are still not at a loss if you use multi-factor authentication. By adding this security enhancement, you are restricting account access for the hacker by giving them another task in account verification. This is more than enough to block a hacker from gaining your user credentials permanently.
- Check the Address Bar: We often click on a website and see where it takes us, but that may eventually redirect us to a malicious site. To avoid fake websites, make sure to check the address bar and see if the lock symbol comes with an authenticated certificate.
Conclusion
Man in the Middle attack has been around for a long time, and it is not going anywhere as long as there are people who can exploit different use cases in real life. So taking necessary precautions and understanding the signs of MITM attack are crucial to mitigate personal data loss. Here, one needs to drive their focus to create a preventive mindset and follow the safety steps regularly.
The opportunities for these cybercriminals are increasing every day with new devices and networks. In the future, we will witness a wide variety of interconnected devices with IoT, which only indicates a rapid growth in such MITM attacks. There may be more advanced security software being developed, but it is always in the best interests to follow some practices daily.

I'm fascinated by the IT world and how the 1's and 0's work. While I venture into the world of Technology, I try to share what I know in the simplest way with you. Not a fan of coffee, a travel addict, and a self-accredited 'master chef'.